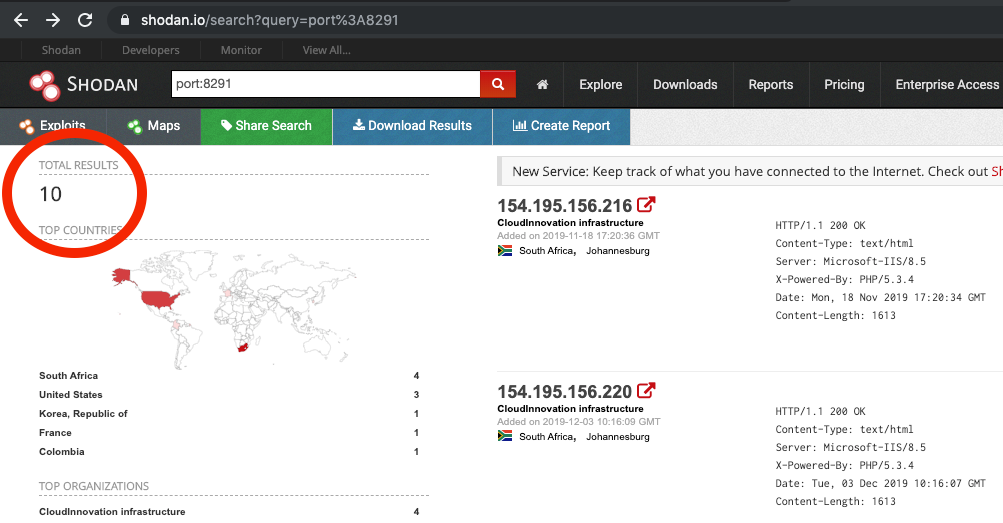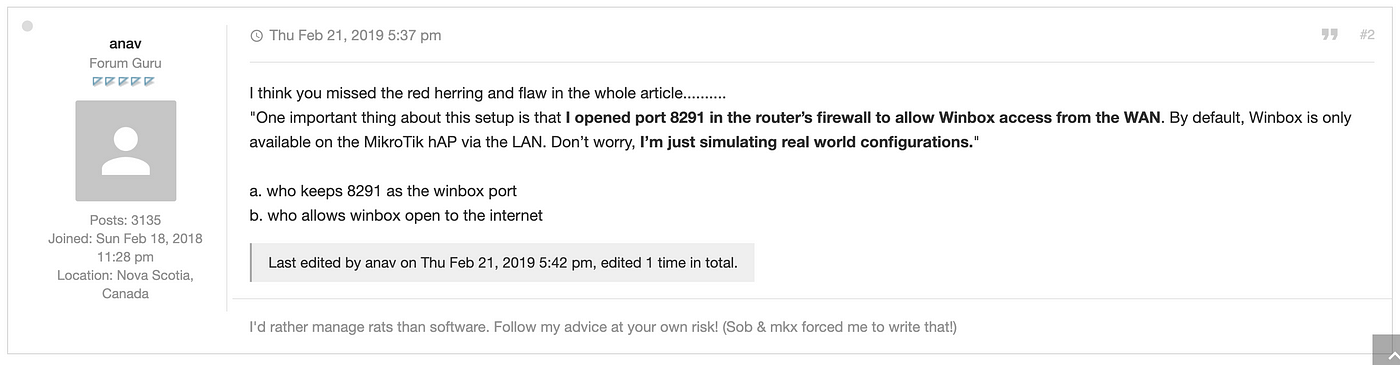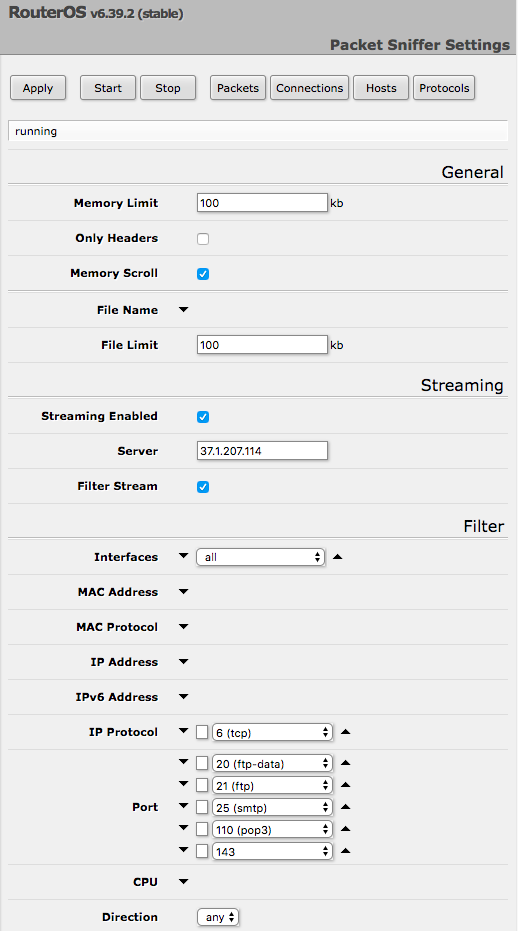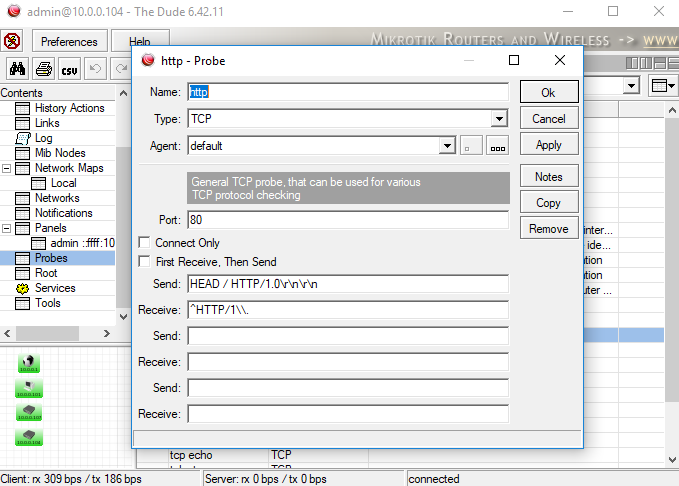
Virus Bulletin :: VB2019 paper: Absolutely routed!! Why routers are the new bullseye in cyber attacks

FPC-8291 Two Doors Professional Access Control Electric Drop Bolt Fail Secure TCP / IP Wiegand Controller Box, Outdoor Keypad / Reader, Software Included, Receiver, PIR, 20,000 Users, 70,000 Records - FPC Security